Are You Ready to Make the Move from ADFS to Azure AD?
With organizations (and Microsoft) increasingly moving from on-premises to cloud-based solutions, the way we handle identity and access management is changing as well. Software we used to rely on for single sign-on access is not necessarily a good fit for our current landscape of remote workers using multiple devices. Is it time for your organization to migrate from Active Directory Federation Services to Azure Active Directory? Here we explain the differences between the two systems, why you should consider migrating, and how to do it with minimum disturbance to your organization.
What are Active Directory Federation Services?
Active Directory Federation Services (ADFS) is a single sign-on on-premises identity service developed by Microsoft to allow the sharing of identity information outside an organization’s network. It can be installed on Windows Server operating systems to provide users with single sign-on access to different systems and applications across organizational boundaries. ADFS uses claims-based access-control authentication. This means users are authenticated based on a set of claims about their identity, which are packaged into a secure token by the identity provider.
However, ADFS also has some significant limitations. The biggest drawback is that you need to have access to your physical servers to access ADFS. If for any reason your servers are inaccessible – fire, power outage, anything – you don’t have access ADFS. This means your organization must also have a back-up DNS server for failover. Other limitations include:
- ADFS do not allow access to shared files or print servers, or Active Directory resources
- ADFS is meant for on-premises environments and does not authenticate through Azure infrastructure; it only authenticates against Active Directory
- ADFS do not authenticate some “older” web applications
- There can be hidden server maintenance costs associated with ADFS
- ADFS require certificate maintenance, meaning planned downtime
- Restricting access for certain groups can be complex with ADFS
- ADFS have a requirement for AD Domain accounts, which would work only on domain-joined devices
What is Azure Active Directory?
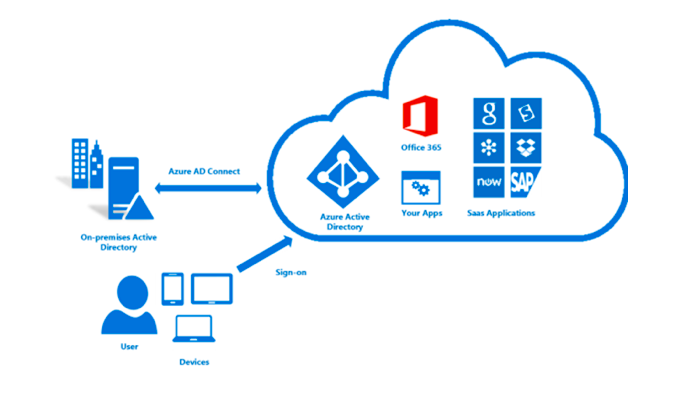
Microsoft introduced Azure Active Directory (Azure AD) as the next evolution of identity and access management. It is Microsoft’s cloud-based identity and access management service. Azure AD provides organizations with an Identity as a service (IDaaS) solution for all their apps both on-premises and cloud-based and allows legacy applications incapable of modern authentication methods to run in the cloud. In this way, each user can use a single identity to access both external resources (like Microsoft 365 and the Azure portal) as well as internal resources (like apps on your corporate network or intranet). With Azure AD, users can access these applications and collaborate together from any platform and any device.
Azure AD has a full suite of identity management capabilities*, including auditing, device registration, multi-factor authentication, and self-service password management.
*Capabilities are based on what licensing level is included in your subscription(s) or has been separately purchased.
Why Migrate App Authorization from ADFS to Azure AD?
For optimal app security, your best approach is to have a single set of unified access controls and policies across your on-premises and cloud environments. By moving all app authentication to Azure AD you will more effectively be able to manage risk and cost, increase productivity, and ensure you are meeting compliance and governance requirements. Further, as Microsoft is increasingly moving to the cloud, it is likely that over time, on-premises-based solutions will be phased out. Let’s take a closer look at some of the reasons you might want to migrate from ADFS to Azure AD:
Reduce Risk
Migrating all your apps to Azure AD consolidates your security solutions, giving you a full view of all risk factors. Using the catalog of apps that are already federated through Azure AD gives your organization control of those apps, as well as the data in those apps. Users will be able to access apps and data more securely using Conditional Access policies, Multi-Factor Authentication, and real-time risk-based Identity Protection technologies. Azure AD also protects privileged user’s access with Just-In-Time admin access.
Once you have your apps migrated, depending on your license, you can connect them using Microsoft Cloud App Security. This can help you take advantage of the benefits of cloud applications while maintaining control of your corporate resources. Microsoft Cloud App Security enables you to investigate activities, files, and accounts as well as implement policies that create governance actions, set data loss prevention and file-sharing controls. You can also create reports that show which cloud apps are being used, by which people, and on which devices.
Save Money
It’s likely you have already paid for Azure AD by way of your Microsoft 365 license.
If your organization is currently using multiple Identity Access Management (IAM) solutions because ADFS does not meet all your needs, migrating to one Azure AD infrastructure you’ve already paid for allows you to significantly reduce IAM costs.
Increase Productivity
For end-users, Azure AD enables a streamlined password and authentication process and makes it easier to engage with users outside your organization (while still letting you maintain control over sensitive apps and data). Employees have access to self-service options and enjoy a consistent experience across apps.
Administrative overhead is also reduced by managing only a single identity for each user across cloud and on-premises environments. It is possible to automate provisioning of user accounts (in Azure AD Gallery) based on Azure AD identities. Plus, you have access to all your apps from the Azure portal.
Address compliance and governance
Azure AD gives you the ability to manage and control the apps your organization is using, as well as data contained in those apps. This means you can ensure compliance with regulatory requirements are met by monitoring application sign-ins through reports that leverage Security Incident and Event Monitoring (SIEM) tools. These reports are available from the Azure portal or APIs and can be used to regularly audit who has access to your applications and remove access to inactive users via access reviews.
How To Migrate App Authentication from ADFS to Azure AD
Planning out your migration from ADFS to Azure AD carefully and clearly is crucial for avoiding mismatched expectations or miscommunications with stakeholders in your organization. An important element to consider right at the start of your authentication migration project is the project team itself. While the physical migration is primarily IT-focused, operations and business users will also need to be involved throughout the process. This will not only help the project team understand the importance of the different apps, but it will help to increase buy-in from organizational stakeholders.
Microsoft recommends thinking of the migration in four phases, to prioritize migrations and achieve success with minimal business impact.
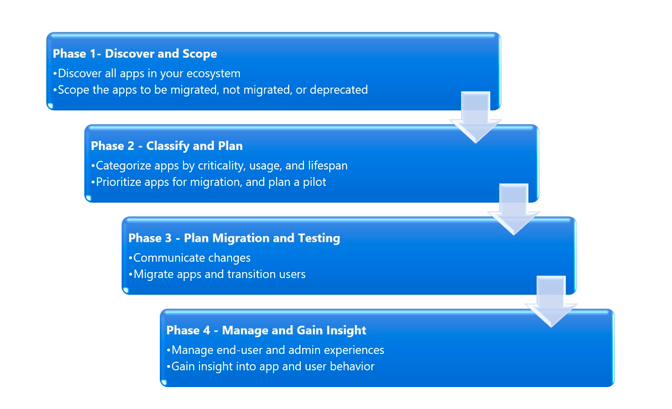
Phase 1: Discover and Scope Apps
In this phase, you begin to prepare for the migration by compiling a list of the apps your organization currently uses, decide which ones to migrate, which (if any) should remain, and which apps to deprecate. While discovering apps, don’t forget about apps that are in development, and make sure to use Azure AD for the authentication of all future apps.
You will also need to gain an understanding of your organization’s entire app ecosystem, including how apps interact, where and how the apps are used, by whom, and on what devices. Seeing the full picture like this helps you evaluate the importance of each app, and ultimately decide whether each app should be migrated or not.
There are a variety of ways to discover the apps in your organization:
- Using ADFS tools like Azure AD Connect Health and AD FS log parsing.
- Using an existing identity provider (IdPs) if in place and migrating away
You will exit Phase 1 with a detailed list of apps that includes:
-
- What systems those apps connect to
- Where and on what devices users access them
- Whether they will be migrated, deprecated, or connected with Azure AD Connect.
Phase 2: Classify Apps and Plan Pilot
Next, once you understand the scope of the apps your organization uses and their technical requirements and dependencies, you can start the process of classifying them, and prioritizing the order in which they will be migrated. One way to think about this is along the axis of business criticality, usage, and lifespan, each of which is dependent on multiple factors that will be unique to your organization.
- Business Criticality – how integral is it to business functions? You can determine this by looking at the number of unique features/functions the app provides, as well as how many users it has.
- Usage – apps with high usage should be classified higher than those with lower usage, as measured by both user volume and user breadth.
- Expected Lifespan – once you have determined business criticality and usage, you can determine the app’s lifespan, and create a prioritization matrix:
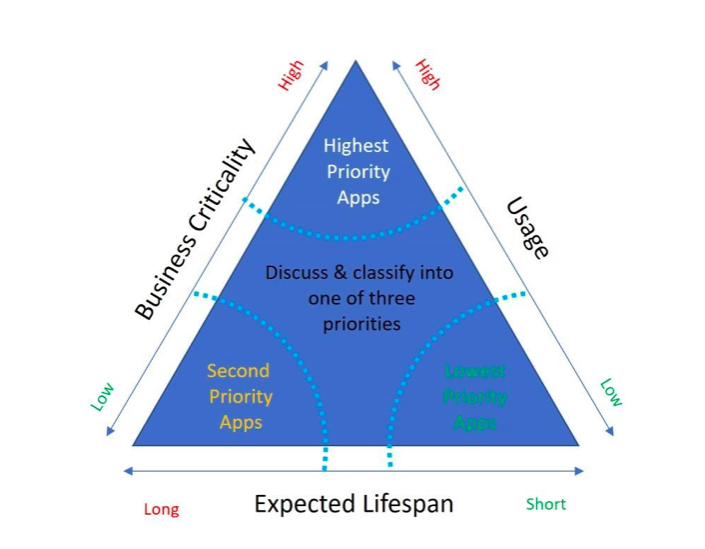
Once you have your apps prioritized, you can decide whether to begin the migration with your lowest priority apps or the highest priority apps based on the specific needs of your organization. Moving lower priority apps first can help to minimize business impact – ideal for organizations that are not experienced in using Azure AD. This lets you gain stakeholder confidence as you continue to migrate the rest of your apps. However, if you have a strict deadline to migrate the apps, the high priority apps should be migrated first. Additionally, establishing a migration schedule within which app owners must engage to have their apps migrated can be beneficial. At the end of this process, you should have a list of all applications in prioritized buckets for migration.
You will exit phase 2 when you:
- Know your apps:
- Have fully documented the apps you intend to migrate
- Have prioritized apps based on business criticality, usage volume, and lifespan
- Have selected apps that represent your requirements for a pilot
- Have business-owner buy-in to your prioritization and strategy
- Understand your security posture needs and the best way to address them
Phase 3: Plan Migration and Testing
The next stage of the process covers how you will physically migrate these applications into the Cloud. Microsoft offers precise tools and guidance to help migrate your apps to Azure AD. Use the tools and guidance below to follow the precise steps needed to migrate your applications to Azure AD:
1. General migration guidance. Use the whitepaper, tools, email templates, and applications questionnaire in the Azure AD apps migration toolkit to discover, classify, and migrate your apps.
2. SaaS applications – See Microsoft’s list of SaaS app tutorials and download the complete Azure AD SSO deployment plan to walk through the end-to-end process.
3. Applications running on-premises – Learn all about the Azure AD Application Proxy and download the complete Azure AD Application Proxy deployment plan to get going quickly.
4. Apps you’re developing – Read this step by step integration and registration guidance.
Post-migration, go to the Azure Portal to test if the migration was a success. Follow the instructions below:
- Select Enterprise Applications > All applications and find your app from the list.
- Select Manage > Users and groups to assign at least one user or group to the app.
- Select Manage > Conditional Access. Review your list of policies and ensure that you are not blocking access to the application with a conditional access policy.
Another key element of this phase is planning rollback. If your migration fails, the best strategy is to rollback and test. Having a planned rollback helps to mitigate migration issues.
You can exit this phase when you have:
- Determined how each app will be migrated
- Reviewed the migration tools
- Planned your testing including test environments and groups
- Planned rollback
- Migrated the apps to Azure AD
Phase 4: Plan Management and Insights
Once your apps are migrated, the main focus is ensuring your users have access to them. The simplest way to do this is to direct them to the MyApps portal. Here, they can access all cloud-based apps, apps you make available by using Azure AD Connect, and apps using Application Proxy provided they have permissions to access those apps. Make sure your apps are accessible on mobile devices, from browser extensions, and at Office.com
The second part of phase 4 is one that is often overlooked. Once apps are migrated, you must ensure that users can securely access and manage them, and that you can access the appropriate insights into usage and app health. Azure AD makes this simple with centralized access to manage your apps. Go to the Azure portal and enable the following capabilities:
- Secure user access to apps. Enable Conditional Access policies or Identity Protection to secure user access to apps based on the user’s device state, location, and more.
- Automatic provisioning. Set up automatic provisioning of users with a variety of third-party SaaS apps that users need to access. In addition to creating user identities, it includes the maintenance and removal of user identities as status or roles change.
- Delegate user access management. Designate selected apps as self-service and assign a business approver to approve access to those apps. Use Self-Service Group Management for groups assigned to collections of apps.
- Delegate admin access. Assign admin roles to your selected user using Directory Roles.
It’s also essential that you monitor app usage and adoption post-migration to detect potential errors. Monitoring all aspects of your app migration can be time-consuming, so agree on some KPIs that you will focus on in your Azure portal.
You are successful in this phase when you:
- Provide secure app access to your users
- Manage to audit and gain insights on the migrated apps
What Kinds of Apps are in the Azure Gallery?
The Azure AD gallery contains thousands of pre-integrated apps, so chances are most of the apps your organization uses are probably already there. This includes both general apps, such as Zoom, Google apps, Cisco Webex, and ServiceNow, as well as industry-specific apps. For example, education-specific apps include Canvas, Blackboard, Brightspace, Clever, OpenAthens, EBSCO, and many more.
Adding an app from the gallery to your Azure AD tenant is simple as long as you have an Azure account with an active subscription, and are either a Global Administrator, Cloud Application Administrator, Application Administrator, or owner of the service principal.
Ready to Make the Move?
Migrating from ADFS to Azure AD is an important step to becoming fully cloud-based, but it can present challenges. Qualifying organizations can avail of complimentary support from Steeves and Associates through Microsoft FastTrack. Get in touch today to find out if your organization qualifies!

