Microsoft 365 Security: Your Questions Answered!
Microsoft has invested significantly in its security solutions over the last number of years, rivalling many third-party cybersecurity providers and that is just the beginning. Microsoft has committed to investing $20 Billion USD to continue to advance its security solutions over the next five years. We want to help identify the tools that are part of Microsoft 365 Security suite and share some expert insights to help you to secure your environment.
What Does Microsoft 365 Security Entail?
To get a quick overview of the different security solutions and services in Microsoft 365 you need to know that there are five main domains that Microsoft maintains:
- Identity access
- Threat Protection
- Unified Endpoint Management
- Data Protection
- Cloud Security
Each of the above domains has dedicated products that can help you to secure your environment. And, if you have unlimited resources and unlimited time you probably want to implement all of these different controls and products, but most organizations don’t. In which case, we recommend that you approach your organization’s cybersecurity based on the most imminent threats, organizational risks and the maturity of your current cybersecurity infrastructure.
Getting Started with Microsoft 365 Security
For those that are just starting out, Microsoft 365 Defender leverages the Microsoft 365 security portfolio to automatically analyze threat data across domains and builds a complete picture of each attack in a single dashboard. Microsoft 365 Defender provides a consolidated feel of all Microsoft 365 security products in one place. All the different portals of the cyber security portfolio that comprise of multiple products, multiple interfaces and control planes are found in this one place and you can use this platform to conveniently switch between them.
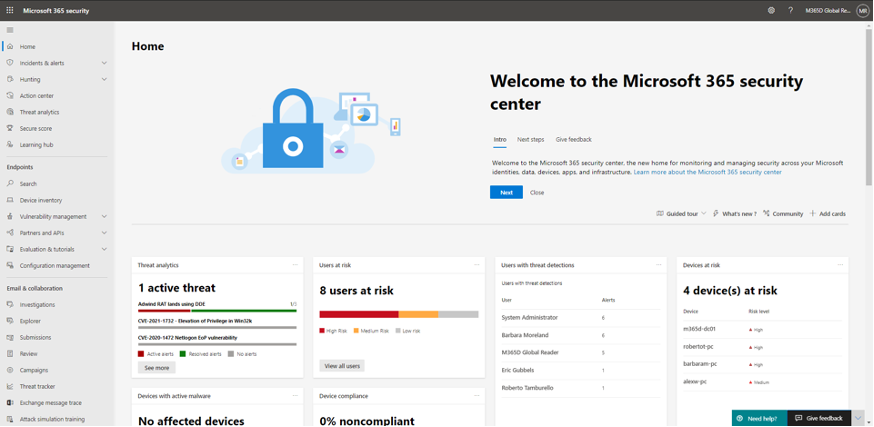
A feature of key importance in the Microsoft 365 Security Center as shown in the above dashboard, is the Microsoft Secure Score. This will give you a baseline of where your organization is currently at in terms of its security posture. The lower the secure score, the greater the opportunities for improvement actions to boost your security score and thus your security posture. Assess your score and utilize the OOTB metrics to compare your organization to other organizations in your industry and review the improvement actions recommended by Microsoft to improve your score.
___________________________________________________________________
Want to See Microsoft Security Solutions in Action?
Take a deep dive into how to plan and implement Microsoft 365 Security, by watching the on-demand webinar highlighting MCAS, Azure Sentinel, Microsoft 365 Defender, and Threat Hunting.
___________________________________________________________________
The Most Recent Questions We’ve Receive About Microsoft 365 Security
When transitioning to Microsoft 365 Security, users often have several concerns. We have answered some of the most recent questions we have received about Microsoft 365 Security below.
Is it Possible to Achieve Defensible Security Without Microsoft 365 E5 Licensing or a Security Add-on?
The first and probably the most significant question out there is about obtaining the right licensing. between licensing levels and how many licenses to purchase for the organization.
- Before you get the Microsoft license for the product you are interested in, we suggest you look at what you’re spending on third party products. It makes sense to review and analyze if you have any renewals coming up for say mail filtering or endpoint protection and asses your spending, as it may make sense to use this funding towards the Microsoft 365 E5/M5 security skew. Also, we would recommend taking a look at any impact on your cybersecurity insurance costs.
- In addition, the number of licenses you purchase depends on the needs of your organization and the industry you fall under. These factors determine the license best suited for you and determine the number of individuals required to monitor and execute your organization’s cybersecurity. Feel free to reach out to us if you need guidance on the exact number of licences for your organization.
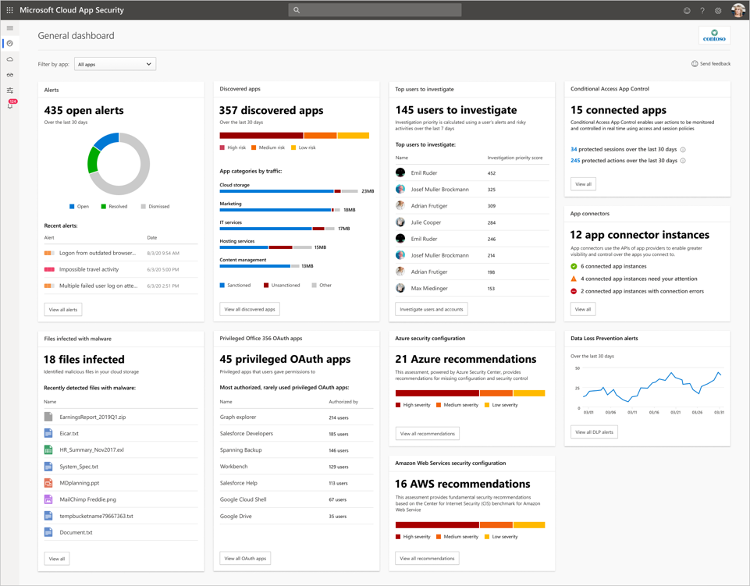
What License Do We Need for Microsoft Cloud App Security?
For a secure cloud infrastructure, you must have visibility into your cloud applications. A tool integral to this is the Cloud Access Security Broker, the Microsoft product name is ‘Microsoft Cloud App Security’. You can monitor applications in real-time with the Cloud App Security API. In case you are wondering how you can get your hands on this product; we are here to tell you how.
- An M3 or M5 license provides access to Microsoft Cloud App Security and you can also buy it as a line item. There’s a great resource called M365 Maps (not Microsoft sanctioned) if you’re looking for a visual representation of the products each license provides access to. Click here for the official details on Microsoft Cloud App Security from Microsoft.
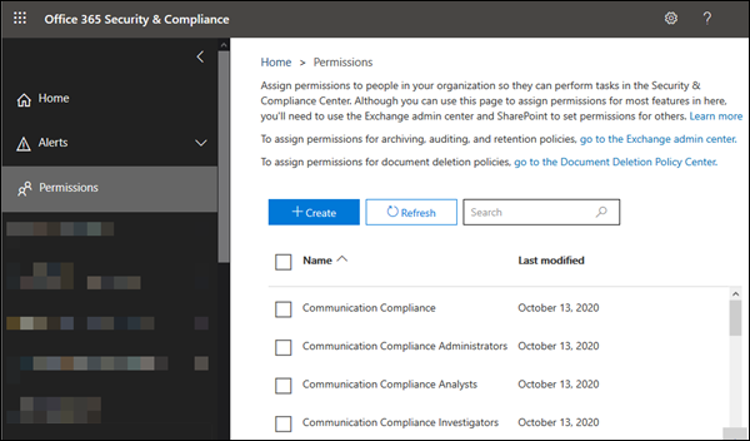
What Permissions Are Recommended for a Security Analyst Level?
As a security analyst, users can make use of different roles depending on hands on they’re going to be.
- It might make sense to start off with the ‘security reader’ permission level, which allows the user to look at all the different security components in Microsoft 365. The limitation here is that the user won’t be able to make changes or perform any actions. So, the next level above that is the ‘security investigator’ role which allows users to perform some actions. If you have a large infrastructure security team then you may want to grant ‘investigator’ level to most of your team so that they can action some of the alerts. You can also go up to the highest access level, which is a ‘security administrator’ role, which enables users to perform all actions.
What’s the Recommended Approach to Training the Security Team on the MS Security Portal?
Training is a crucial part of getting used to the Microsoft 365 security interfaces and the overall control pane across the different services. So, where to look and where to begin?
- Microsoft has some training resources within the Defender console itself. These resources are kept up to date and have a variety of videos and documents that users can go through. Other than the out-of-the-box resources, the support and expertise of an organization such as Steeves and Associates can go a long way in making sure your team is equipped to effectively operate across the Microsoft 365 security framework.
What Are the Barriers to Transitioning to the Microsoft 365 Security Portal?
Transitioning from one security portal to another is not usually a seamless experience. This is also the case when you move over to the Microsoft 365 security portal. Thus, it is best to be aware of the barriers that may come your way in advance and take the necessary steps to overcome them.
- The biggest hurdle is that it’s a new technology! Your security team needs identify the new components that are available in cloud and the new security controls and technologies that are available. The best way to approach it is to build on the existing security knowledge. It is important to understand that Microsoft 365 security is dynamic and subject to change on a quarterly basis, making it crucial to learn, unlearn and learn time and again. The main idea to ease the transition is to stay abreast of the latest updates and keep up with the resources.
Are there any Privacy Concerns about using Microsoft CASB outside of Canada?
Privacy concerns are common among public bodies with their tenants hosted in Canada, while the Microsoft Cloud App Security is hosted in the United States. It depends on the regulations that govern your institution and thus it becomes important to evaluate the situation on a case-by-case basis. Feel free to reach out to us directly with your specific concerns for a more elaborate discussion.
Get the Right Security Partner
That’s not all, there is so much to Microsoft 365 Security that is not as easy to summarize in a blog. Microsoft 365 Security is a broad and complex solution. To be able to successfully navigate through the products and make the most of their features, you need a trusted partner by your side. That’s where Steeves and Associates comes in. Get involved with Steeves’ Security Workshops and we will guide you through the nuances of keeping you cloud environment as secure as possible with the right means. Reach out to us to commence your Microsoft 365 security journey today.

